GLI® Secure Identity & Access Management (IAM)
In today’s hyperconnected environments cloud platforms, third-party integrations, and remote work are the norm, knowing exactly who has access to your systems is no longer optional.
Overview
The structure, visibility, and control organizations need to secure critical data and systems without slowing down operations.
Identity and Access Management (IAM) provides the structure, visibility, and control organizations need to secure critical data and systems without slowing down operations.
GLI Secure delivers IAM solutions supported by a team with deep experience in complex, highly regulated industries. This shared expertise brings operational consistency, disciplined security practices, and a practical understanding of how to balance strong access control with day-to-day business needs.
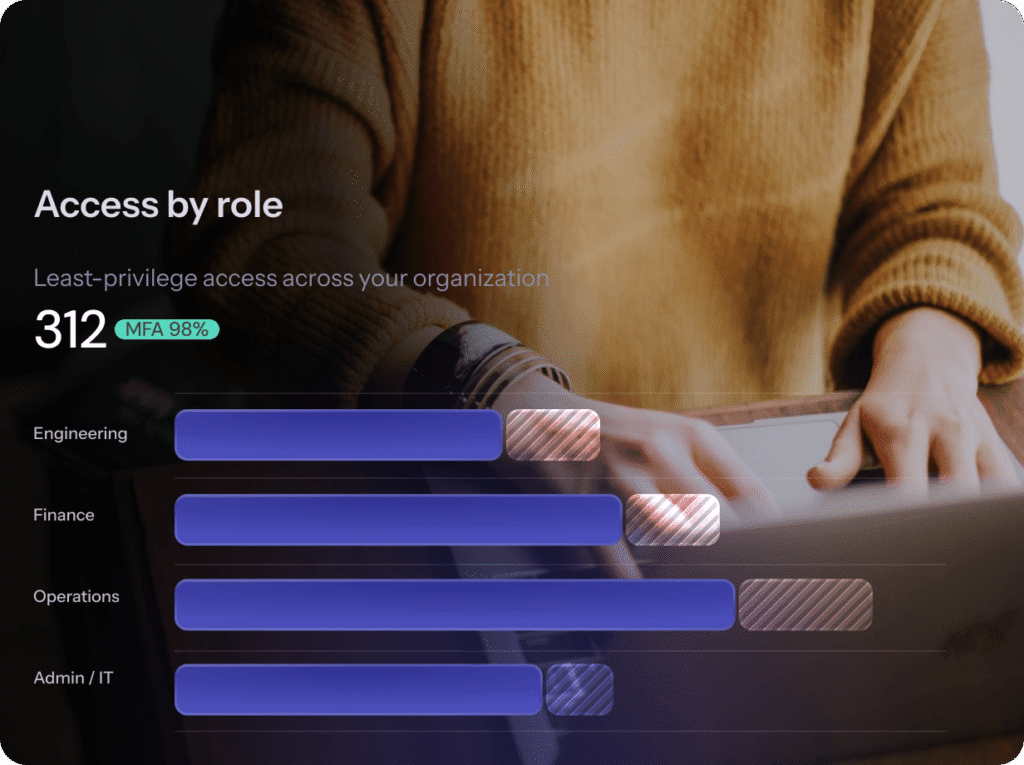
At its core, IAM ensures that the right individuals have the right access to the right resources at the right time. By enforcing least-privilege access, users are granted only the permissions necessary to perform their roles, which significantly reduces the risk of unauthorized access or insider threats. This is especially critical for organizations managing sensitive data, financial transactions, or compliance-driven environments.
Ready to begin
Explore IAM Solutions
Modern IAM
Modern IAM solutions go beyond simple username and password controls.
Multi-factor authentication (MFA) adds an essential layer of security by requiring users to verify their identity through multiple methods, such as a password combined with a mobile device or biometric factor. This significantly reduces the risk of credential-based attacks, including phishing and password reuse.
An IAM framework shaped by this level of expertise also delivers:
Centralized identity governance across on-premises and cloud environments.
Automated provisioning and deprovisioning to ensure access is updated in real time as roles change.
Continuous monitoring and auditing that improves visibility into user activity and supports compliance requirements such as NIST and ISO.
Privileged access controls that help protect high-risk accounts from targeted attacks.
Operational Resilience
For organizations operating in complex environments, IAM is not just a security control but a foundational layer of operational resilience.

As systems become more interconnected, unmanaged identities can quickly become one of the most exposed attack surfaces.
A Strategic, Proactive IAM Approach
Stronger security posture, improved operational efficiency, reduced compliance risk.
With guidance from a cybersecurity team shaped by deep experience supporting highly regulated, high-risk industries, your organization can move beyond reactive access management and adopt a more strategic, proactive IAM approach.
The result is...
Stronger security posture, improved operational efficiency, reduced compliance risk, and greater confidence in every digital interaction.